The Issue: The Exorbitant Price of Reset Support and Password Fatigue
Modern authentication systems are expected to provide secure access without slowing users down or increasing operational overhead. However, password-based authentication continues to create frequent reset requests, login friction, and security challenges for enterprises. Poor password practices, phishing, and credential misuse still remain common because users are expected to manage increasingly complex authentication requirements. At the same time, organizations spend time and resources managing password-related issues instead of improving user access and security experiences through Magic Link Authentication.
The Answer: Using Azure AD B2C to Create a Robust Magic Link Authentication System
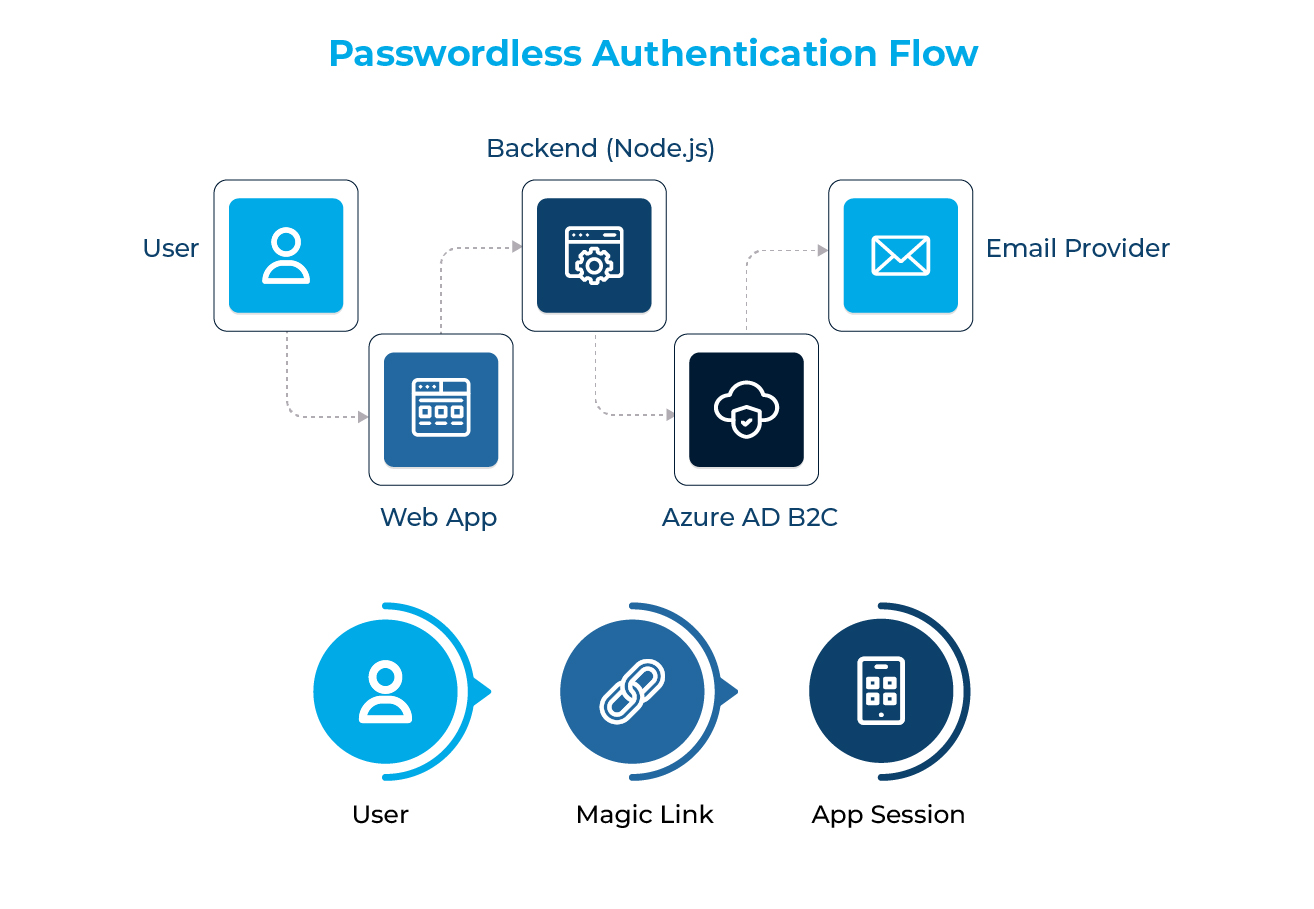
Passwordless authentication through magic links eliminates the weakest link in the identity chain: passwords stored in human memory.
A magic link authentication system replaces passwords with:
- A short-lived, cryptographically signed token
- Delivered through a verified communication channel such as email
- A token valid for a single authentication session
Using Azure Active Directory B2C provides enterprise-grade capabilities:
- Standards-based identity flows (OIDC / OAuth 2.0)
- Policy-driven authentication logic
- Native MFA, conditional access, and audit logging
Identity Verification: Using Node.js and Graph API as a Gatekeeper
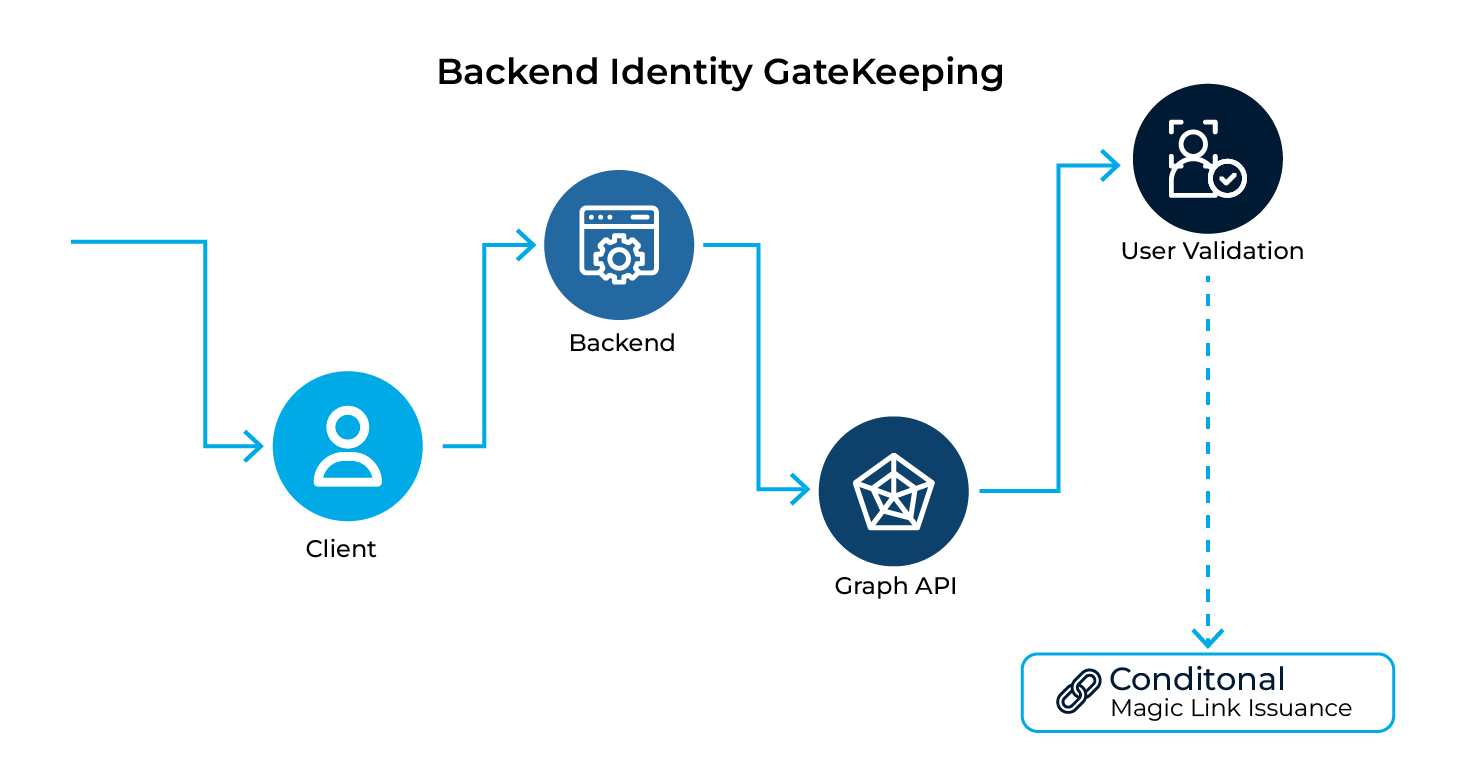
A magic link system is only as secure as its identity verification boundary. This is where many implementations fail because they are overly permissive. The backend implemented in Node.js acts as a gatekeeper rather than an identity provider.
Why Backend Validation Is Critical
The backend should:
- Verify whether the email exists in B2C
- Enforce tenant-level policies such as user state and domain limitations
- Decide whether to issue a magic link instead of simply generating one
The backend can use the Microsoft Graph API to:
- Securely query user objects
- Verify account state, such as enabled, verified, or external identity
- Prevent identity exposure through client-side logic
The User Journey: Creating a Seamless Transition Between Web, Email, and App
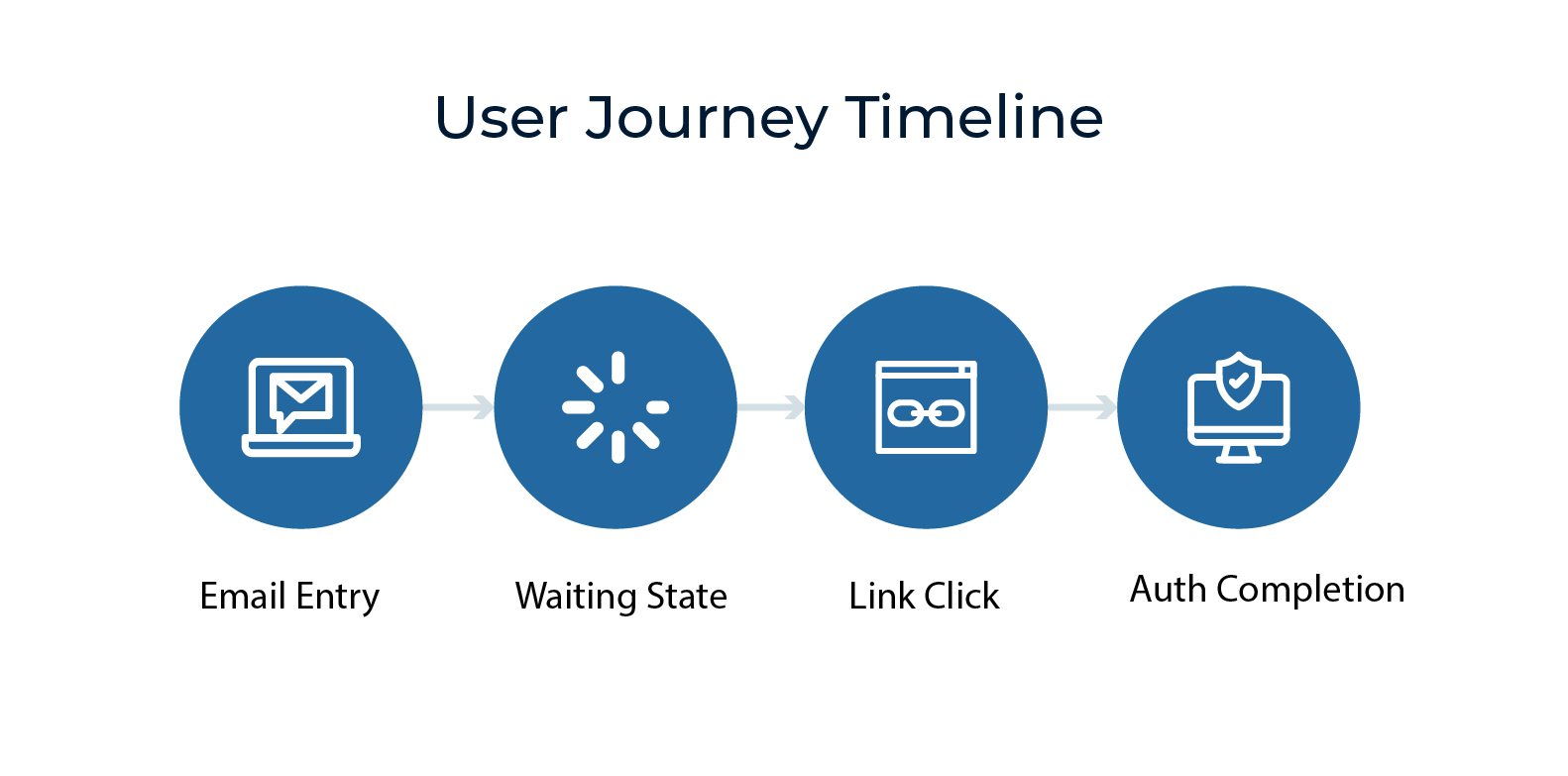
Journey continuity determines whether a magic link system succeeds or fails, not just token security or the quality of backend implementation. A passwordless flow quickly becomes frustrating when consistency is disrupted by context loss, unnecessary redirects, page reloads, or unclear state changes.
Even if authentication technically succeeds, the user experience fails when users are forced to switch apps, restart their browsers, or re-enter information without understanding why. Because a well-designed magic link experience maintains state across web, email, and app boundaries so that authentication feels smooth rather than procedural.
A production-grade flow must ensure:
- The magic link deep-links back to the correct application state
- Tokens are bound to:
- Device context
- Browser session
- Expiration policies
- Expired or replayed links fail securely without exposing sensitive details
Securing Passwordless Magic Link Authentication with Azure AD B2C
Building a custom identity system is rarely a mark of engineering excellence; it is often a fast track to compliance risk and long-term maintenance challenges. Security standards, audits, logging requirements, and regulatory expectations are unforgiving, and identity systems are among the easiest places to make costly mistakes.
What appears to be control in the short term often becomes technical and legal debt over time.
Azure AD B2C offers:
- GDPR, SOC 2, ISO 27001, and regional compliance support
- Integrated sign-in records and audit trails
- Native support for MFA escalation and conditional access policies
From a security architecture perspective:
- Tokens are revocable and short-lived
- Authentication logic is policy-driven instead of code-driven
- This approach minimizes the potential impact of credential compromise
Scaling Up: Making Authentication Strategy Future-Proof
Magic links should be viewed as the beginning, not the end, of a passwordless strategy. They remove immediate usability and security challenges associated with passwords, but their true value lies in enabling future authentication models.
Organizations can gradually adopt stronger approaches such as passkeys, device-bound credentials, and adaptive risk-based authentication without disrupting user workflows or rewriting applications. In this way, magic links represent a transition from brittle, static authentication systems to adaptive identity architectures capable of evolving alongside threat models and user expectations.
A well-designed system should evolve toward:
- Device-specific credentials (Passkeys/FIDO2)
- Risk-based authentication policies
- Progressive profiling instead of static sign-up forms
Azure AD B2C enables organizations to:
- Change authentication methods without switching applications
- Introduce MFA only when risk levels increase
- Support multi-channel identities such as phone, email, social, and enterprise accounts
Conclusion
Passwordless authentication is no longer just an alternative authentication method; it is becoming the foundation for future-ready digital identity strategies. As organizations move toward passkeys, adaptive authentication, and device trust models, identity systems must become more flexible, intelligent, and risk-aware.
Magic Link Authentication, combined with Azure AD B2C, creates a scalable framework that supports this evolution without disrupting applications and user experiences. Organizations that modernize their authentication architecture today will be better positioned to reduce security risks, simplify access experiences, and adapt to the next generation of identity and access management requirements.





