Application Programming Interface (API) is a software intermediary with a set of rules allowing applications and computers to communicate with each other using requests and responses. Cloud applications communicating with servers or operating systems are some examples of API-based interactions.
APIs are needed to increase productivity and to allow data transfer between software components, applications, operating systems, and people by building programmatic interactions. Using APIs, we can improve connectivity, marketing, and collaboration.
What is API Security?
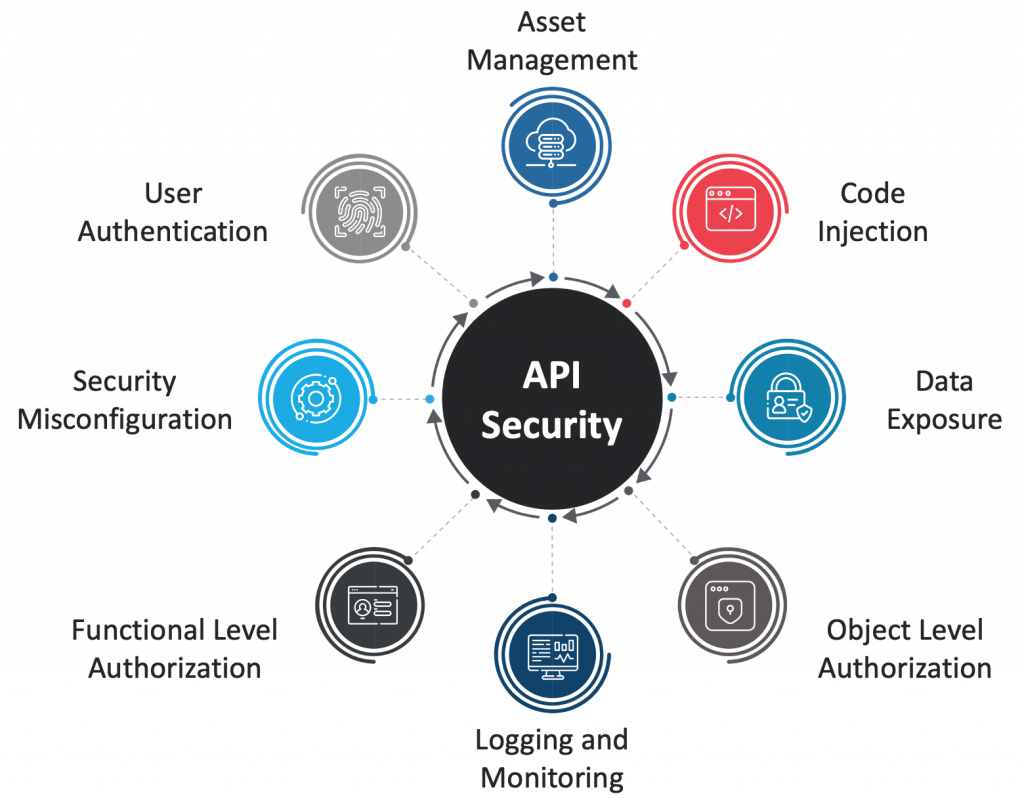
API security is the process of protecting APIs from malicious attacks or misuse. As APIs are very commonly used with sensitive information, they are becoming a primary target for attackers. API Security includes API access control and privacy, as well as the detection and remediation of attacks on APIs through API reverse engineering.
APIs may have vulnerabilities like user authentication, object and function level authorization, code injection, lack of rate limiting, security misconfiguration, and asset management. Organizations must regularly test APIs to identify vulnerabilities and address these vulnerabilities using best security practices.
Why is API Security Important?
API development has increased astronomically in the past few years, as the APIs are used in almost all the applications, fueled by digital transformation along with the role played by APIs in both mobile apps and IoT devices. This increased demand for APIs is making its security a top concern.
API security is needed to avoid risks like excessive data exposure, data breaches, and security misconfiguration and to protect your API keys, passwords, and usernames.
How do I Secure My API?
- Encrypting data through TLS (Transport Layer Security)
- Access Control
- Throttling sensitive information in the API communication
- Remove unnecessary information
- Hashing passwords
- Validating data
- Securing API by establishing an HTTP connection
What Does API Security Need?
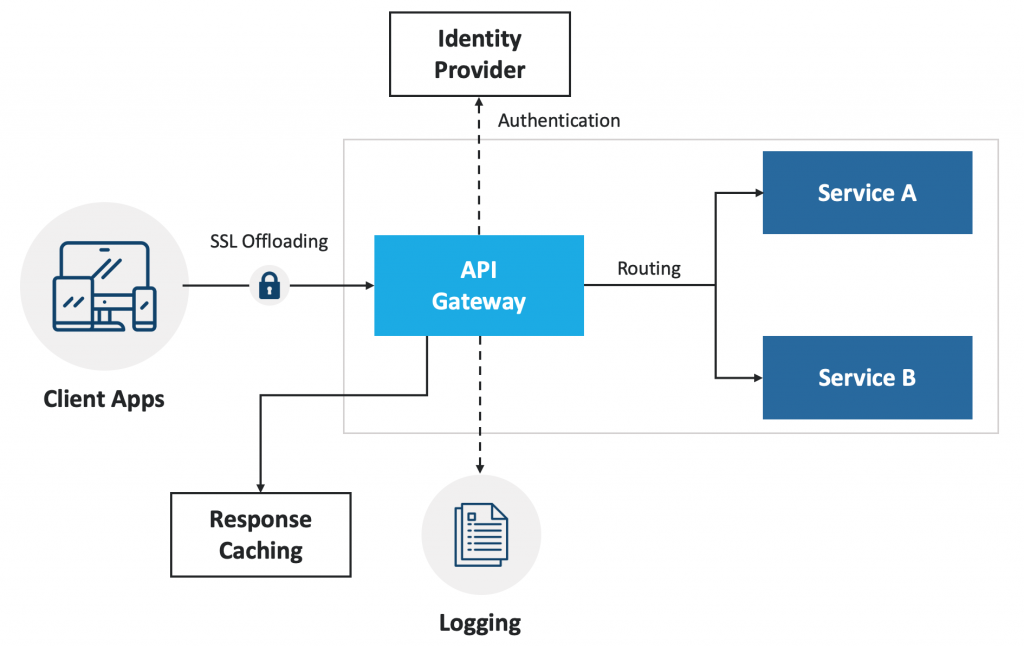
API security as a practice overlaps various systems and teams. Any authentication related information like email address, password, OAuth access token, and API token is required to provide security to an API.
API security will contain network security concepts like auditing/monitoring, identity-based security, throttling sensitive information, data security, and rate-limiting. Different methods of authentication set the authorization header differently.
How Does API Security Work?
- Authentication: Checks the identity of an end-user. All the application malfunctioning attempts are blocked at the application level
- Authorization: Determines the resources an identified user can access
- Another layer of security: An extra layer of security is created between the client and data, by throttling sensitive information in the API response
API Security Best Practices
In the end, security is everybody’s job. APIs related to sensitive information, databases, and backend services must be protected from attackers. HTTP basic authentication needs to be prevented from displaying prompts for images.
There are many best practices that can be applied in order to secure an API and below are a few of them,
- Inventorying API
- API Access Control
- Threat Detection API Security
- Testing Monitoring and Analytics Across API data
- Continuous Auditing and Incident Response
Advantages with API Security
- Encrypt traffic/data using TLS
- Don’t expose more data than necessary
- Strong authentication and authorization solutions are used
- Prioritize security
- Inventory and manage your APIs
- Practice the principle of least privilege
- Remove information that’s not meant to be shared
- Validate input
Nowadays, every business has API threats like breaches of backend systems, degrading API performance, and exposure of sensitive data. So, there is a need to build an architecture that ensures APIs are constantly being monitored and tested to reduce risk levels before attackers misuse the API data.